By Anastasios Arampatzis
Cloud adoption continues to thrive, providing convenience, cost savings, and near-permanent uptimes for organizations compared to on-premises infrastructure. At the same time, threat actors continue to target cloud environments regardless of organization size. Shifting to a cloud model requires a security approach different from that of traditional deployments. A key factor to successful deployment and management of cloud environments is for organizations to understand how threat actors can target them, and how to avoid common pitfalls that leave the cloud vulnerable.
Cloud vulnerabilities on the rise
Understanding the vulnerabilities that threaten the organizations in the cloud is crucial because, as IBM Security indicates, they are on the rise. The 2021 IBM Security X-Force Cloud Threat Landscape Report highlights that cloud vulnerabilities are growing in number, totaling over 2,500 vulnerabilities, a 150% increase in the last five years.
Findings from the same report show that the severity of cloud-targeting vulnerabilities has grown significantly in recent years, likely due to threat actors’ realization that organizations are increasing their use of storing their critical data in multi-cloud environments. Cloud environments are heavily traveled data highways and are a lucrative target for threat actors.
What are the common cloud vulnerabilities?
IBM X-Force Incident Response Team analyzed cases involving cloud breaches and identified the most commonly exploited vulnerabilities and misconfigurations. These include:
Misconfigured resources
Virtual machines and other resources with default security settings were erroneously exposed to the Internet. This included misconfigured platforms and insufficiently enforced network controls that exposed internal services directly to the Internet, such as the Remote Desktop Protocol (RDP) on Microsoft platforms. IBM’s analysis of dark web markets found that RDP accounted for the access vector in over 70% of cloud resources offered for sale on the dark web.
Insecure public APIs are a pervasive problem because they are very common and also allow external tools to interact with cloud functionalities, including access to data. The IBM X-Force IR team found that API credential exposure through public code repositories frequently accounted for threat actor access into cloud environments.
Another major contributor to data breaches in the cloud is unsecured resources that are unintentionally exposed to the internet. These cases include misconfigured object storage services which were found with insufficient hardening and inadequate security controls. The prevalence of Shadow IT can be a key reason for many misconfigured resources.
Lack of strong access control
Insufficient access control mechanisms, such as a lack of multi-factor authentication (MFA) for SaaS solutions and federated services with publicly accessible landing pages, is a commonly observed vulnerability. Attackers using stolen or compromised credentials can authenticate themselves into an account without additional hurdles.
Improper permissions further exacerbate compromises caused by successful password spraying attacks. This sort of attack is easily automated and can scale to target many organizations at once. Once an attacker manages to use a compromised password, their impact is greater in direct proportion to the user’s privilege levels.
Lack of network segmentation
Insufficiently segmented virtual networks and promiscuous trust relationships between on-premises and cloud computing environments are among the top three vulnerabilities in the cloud. A compromise in the cloud can enable further lateral movement across systems. Threat actors compromise end-users or systems hosted on-premises and pivot to a cloud environment. This type of compromise can allow threat actors to deepen their hold on organizations and compromise even more organizational resources.
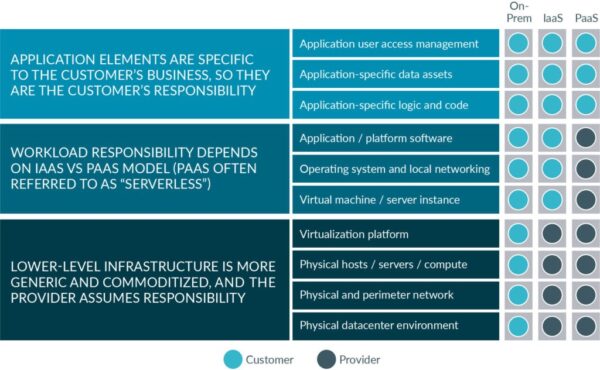
Why does that matter? The Shared Security Responsibility Model
Understanding the most common vulnerabilities in the cloud is important because ultimately it is the cloud customer – the organizations moving to the cloud – who is responsible for the security in the cloud. This is the shared security responsibility model, which means that an organization’s security team maintains some responsibilities for security, while the provider takes some responsibility, but not all. The key to a successful cloud security implementation is understanding where your provider’s responsibility ends, and where yours begins.
In the AWS Shared Security model, AWS claims responsibility for “protecting the hardware, software, networking, and facilities that run AWS Cloud services.” Microsoft Azure claims security ownership of “physical hosts, networks, and data centers.” Both AWS and Azure state that your retained security responsibilities depend upon which services you select.
The following diagram provides a high-level, vendor-agnostic, conceptual view of a shared responsibility model.