Cyber Security in the Shipping Industry
With more than 90% of the world’s trade being carried by shipping, according to the United Nations’ International Maritime Organization, the maritime industry is an attractive target for cyber attackers. The European Union has recognized the importance of the maritime sector to the European and global economy and has included shipping in the Network and Information Systems (NIS) Directive, which deals with the protection from cyber threats of national critical infrastructure.
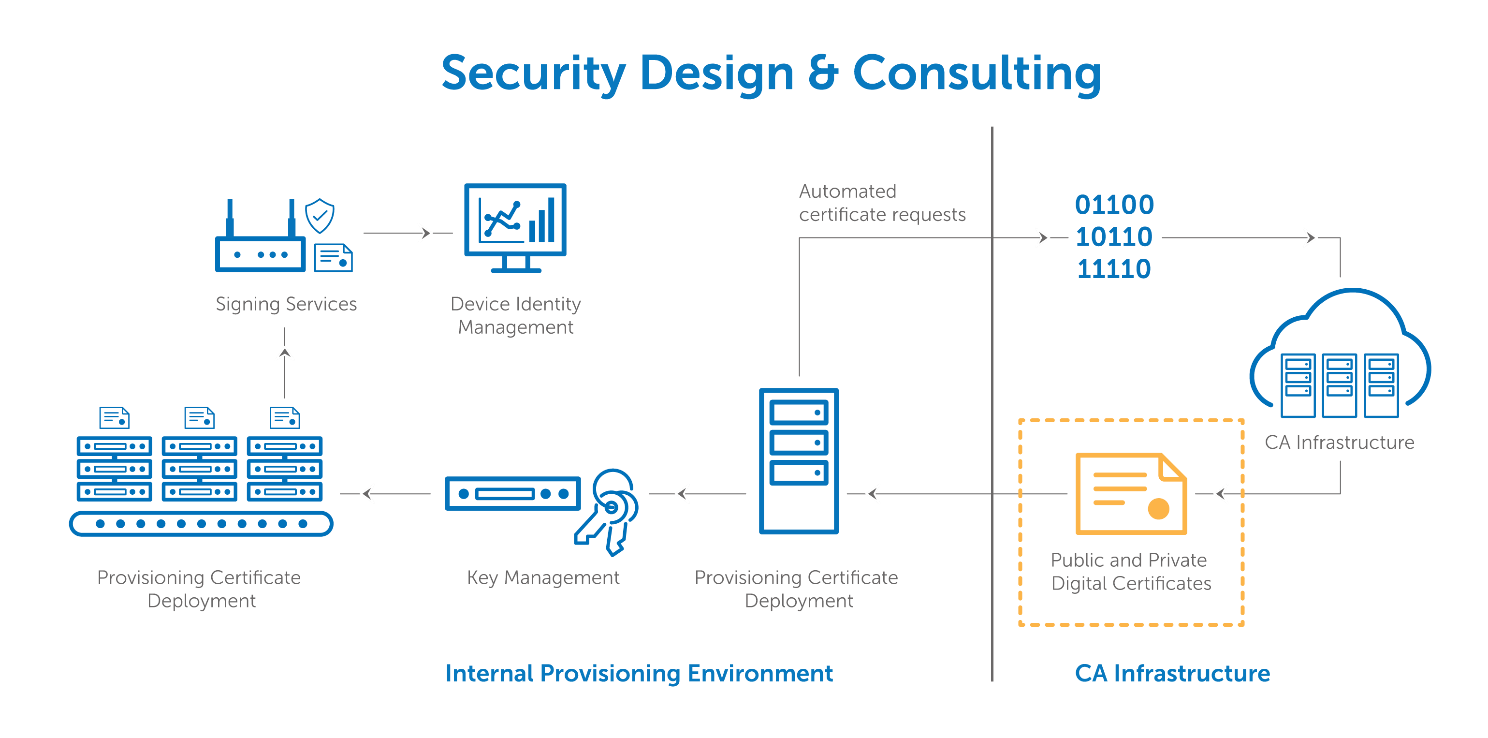
Ships are increasingly using systems that rely on digitalization, integration, and automation. While the IT world includes systems in offices, ports, and oil rigs, the OT world is used for a multitude of purposes, such as controlling engines and associated systems, cargo management, navigational systems, administration, etc.
The OT systems used aboard include:
- Vessel Integrated Navigation System (VINS)
- Global Positioning System (GPS)
- Satellite Communications
- Automatic Identification System (AIS)
- Radar systems and electronic charts