
by Anastasios Arampatzis
Modern organisations need to be resilient not only to maintain business continuity during and after a cyber incident, but looking at a broader context, to be able to withstand and adapt to changes of their business environment. The COVID-19 pandemic only proved the importance of cyber resilience.
To achieve that, organisations need to adopt and implement certain techniques, such as network segmentation, privileges restriction, and asset inventory, to meet the objectives and characteristics of being a cyber resilient organisation.
However, becoming cyber resilient is not enough. As the business environment is changing constantly, new threats and challenges being introduced almost daily and new technologies and systems proliferating, there is a need to assess the level of cyber resiliency. This assessment cannot be a one-off process, rather a continuous one which will allow the organisation to identify gaps, realign their processes and practices and re-evaluate the effectiveness and efficiency of new procedures.
What is Cyber Resilience Review?
The CERT Division at Carnegie Mellon University’s Software Engineering Institute has developed the CERT Resilience Management Model (CERT-RMM), which is a capability-focused maturity model for process improvement, and it reflects best practices from industry and government for managing operational resilience across the disciplines of security management, business continuity management, and information technology operations management.
Based on the CERT-RMM model, the US Department of Homeland Security (DHS) has developed the Cyber Resilience Review (CRR) process, which seeks to understand the cybersecurity management of services, and their associated assets, that are critical for an organisation’s mission success. The CRR focuses on protection and sustainment practices within key areas that typically contribute to the overall cyber resilience of an organisation. The CRR measures essential cybersecurity capabilities and behaviours to provide meaningful indicators of an organisation’s operational resilience during normal operations and during times of operational stress.
It has to be stressed that a CRR reflects an organisation’s capabilities only at the time of the assessment. Even though certain aspects of the review indicate the organisation’s ability to sustain cybersecurity practices over time, the organisation should not rely on the assessment results as a conclusive expression of the organisation’s cybersecurity capability in the future.
The 10 domains of cyber resilience assessment
A cyber resilience review assumes that an organisation deploys its resources (people, data, technology, and facilities) to support specific mission critical services. Based on this principle, the review evaluates the maturity of an organisation’s capacities and capabilities in performing, planning, managing, measuring and defining cybersecurity capabilities across 10 domains:
- Asset Management
- Controls Management
- Configuration and Change Management
- Vulnerability Management
- Incident Management
- Service Continuity Management
- Risk Management
- External Dependency Management
- Training and Awareness
- Situational Awareness
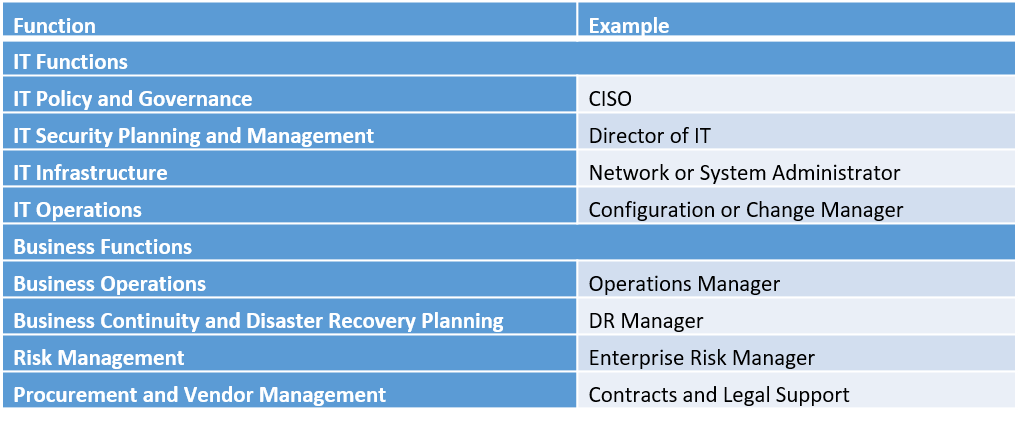
For a cyber resilience review to be effective, it has to be conducted by a multidisciplinary team representing business, operations, security, information technology, and maintenance areas, including those responsible for the functions shown in the following table:
Overview of a cyber resilience review
Each of the domains above represent important capabilities that contribute to the cyber resilience of an organisation. The paragraphs below present a brief overview of the purpose of each domain.
Asset Management. The Asset Management domain establishes a method for an organisation to plan, identify, document, and manage its assets, which are defined as its people, data, technology and facilities.
Controls Management. Internal control is a governance process used by an organisation to ensure effective and efficient achievement of organisational objectives and to provide reasonable assurance of success. The Controls Management domain presents a way for the organisation to identify control objectives and establish controls to meet those objectives. The Controls Management domain also addresses the importance of analysing and assessing those controls to ensure that the process is constantly being improved.
Configuration and Change Management. The domain addresses how an organisation can implement processes and procedures that manage assets and ensure that changes made to those assets are minimally disruptive to the organisation.
Vulnerability Management. A Vulnerability Management process identifies and analyzes vulnerabilities before they are exploited and informs the organisation of threats that must be analyzed in the risk management process to determine whether they pose tangible risk to the organisation based on the organisation’s risk tolerance.
Incident Management. The Incident Management domain examines an organisation’s capability to recognize potential disruptions to their operating environment, analyze them, and determine how and when to respond.
Service Continuity Management. The process of assessing, prioritizing, planning and responding to, and improving plans to address disruptive events is known as service continuity. The goal of service continuity is to mitigate the impact of disruptive events by utilizing well-established plans that facilitate consistent continuity of the critical services.
Risk Management. Risk management is a foundational activity for any organisation and is practiced at all levels, from the executives down to individuals within business units. The cyber resilience review focuses on risks to cyber-enabled operations that have the potential to interrupt delivery of critical services. While the review focuses on operational risk, it is important to note that operational risk management is effective only through a comprehensive and holistic approach.
External Dependencies Management. The outsourcing of services, development, and production has become a normal part of operations for many organisations because it can engage specialized skills and equipment at a cost savings over internal options. The External Dependencies Management domain presents a method to identify and prioritize those external dependencies and then focus on managing and maintaining those dependencies.
Training and Awareness. The domain focuses on the processes by which an organisation plans, identifies needs for, conducts, and improves training and awareness to ensure the operational cyber resilience requirements and goals are known and met. The purpose of the training and awareness activities is to make staff members aware of their role in the organisation’s cyber resilience posture. Staff members should also receive specific training to enable them to perform their roles in managing organisational cyber resilience.
Situational Awareness. Situational awareness activities are performed throughout the organisation to provide timely and accurate information about the current state of operational processes. Activities must support communication with a variety of internal and external stakeholders to support the resilience requirements of critical services.
How to improve cyber resilience posture
A cyber resilience review provides a better understanding of an organisation’s cybersecurity posture. The review provides:
- An improved organisation-wide awareness of the need for effective cybersecurity management
- A review of capabilities most important to ensuring the continuity of critical services during crisis
- A verification of management success
- A catalyst for dialog between participants from different functional areas within an organisation
- A comprehensive final report that maps the relative maturity of the organisational resilience processes in each of the 10 domains, and that includes improvement options for consideration, using recognized standards and best practices
The organisation may use the cyber resilience review report to create an action plan for addressing weaknesses and leveraging the strengths identified. The report can be used as a baseline for initiating a data-driven process improvement project, based on the process depicted on the figure below.
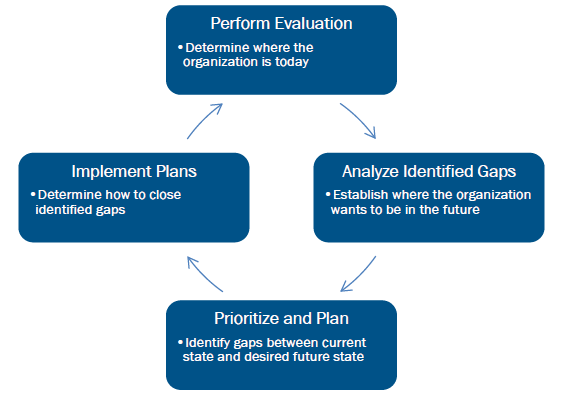
While analysing identified gaps, it is not optimal for an organisation to strive to achieve the highest maturity level in all domains. The organisation should instead determine the level of cyber resilience maturity for each domain that best enables it to meet its business objectives and cybersecurity strategy.
After the gap analysis is complete, the organisation should prioritise the actions needed to fully implement the practices that enable the achievement of the desired capability in specific domains. The prioritisation should be done using criteria such as how gaps affect organisational objectives and critical infrastructure, the criticality of the business objective supported by the domain, the cost of implementing the necessary practices, and the availability of resources to implement the practices. A cost-benefit analysis for gaps and activities can inform the prioritisation of the actions needed.
Next, the organisation should develop a plan to address the selected gaps. For the plan to succeed, organisations must provide adequate resources, including people with the necessary skills to accomplish the planned tasks and an adequate budget. In addition, the organisation must continue supporting the execution of the plan by tracking progress and recognizing accomplishments.
How ADACOM helps
ADACOM has a well-established approach to information resilience, supported by a robust implementation framework. We follow a holistic approach towards protecting all types of sensitive information, in all phases of the information lifecycle throughout all business verticals, regardless of the underlying business and technology ecosystem. Our aim is to maximize the resilience of critical business information and keep information trustworthy even when the organisation is under stress.
ADACOM’s Digital Resilience Readiness Service, undertakes an assessment of the Digital Resilience controls effectiveness & maturity, and provides Organizations with a Roadmap and a Strategy for Digital Resilience enhancement.
Digital Resilience Readiness Service includes the following:
- Assessment of the level of effectiveness and maturity of of the security controls related to cyber resiliense
- Incident Management & Breach Readiness Assessment
- Assessment of the Insider Threat
You may learn more by contacting our experts
