Attackers were preparing to attack dozens of U.S. corporations, including eight Fortune 500 companies.
UPDATE June 30: Further investigation by Symantec has confirmed dozens of U.S. newspaper websites owned by the same parent company have been compromised by SocGholish injected code. Some of the organizations targeted by WastedLocker could have been compromised when an employee browsed the news on one of its websites. Symantec has notified the company and it has now removed the malicious code.
Symantec, a division of Broadcom, has identified and alerted our customers to a string of attacks against U.S. companies by attackers attempting to deploy the WastedLocker ransomware (Ransom.WastedLocker) on their networks. The end goal of these attacks is to cripple the victim’s IT infrastructure by encrypting most of their computers and servers in order to demand a multimillion dollar ransom. At least 31 customer organizations have been attacked, meaning the total number of attacks may be much higher. The attackers had breached the networks of targeted organizations and were in the process of laying the groundwork for staging ransomware attacks.
WastedLocker is a relatively new breed of targeted ransomware, documented just prior to our publication by NCC Group, while Symantec was performing outreach to affected networks. WastedLocker has been attributed to the notorious “Evil Corp” cyber crime outfit. Evil Corp has previously been associated with the Dridex banking Trojan and BitPaymer ransomware, which are believed to have earned their creators tens of millions of dollars. Two Russian men who are alleged to be involved in the group have open indictments against them in the U.S.
The attacks begin with a malicious JavaScript-based framework known as SocGholish, tracked to more than 150 compromised websites, which masquerades as a software update. Once the attackers gain access to the victim’s network, they use Cobalt Strike commodity malware in tandem with a number of living-off-the-land tools to steal credentials, escalate privileges, and move across the network in order to deploy the WastedLocker ransomware on multiple computers.
Discovery
The attacks were proactively detected on a number of customer networks by Symantec’s Targeted Attack Cloud Analytics, which leverages advanced machine learning to spot patterns of activity associated with targeted attacks. The activity was reviewed by Symantec’s Threat Hunter team (part of Symantec’s Endpoint Security Complete offering) who verified it and quickly realized it corresponded closely to publicly documented activity seen in the early stages of WastedLocker attacks.
This discovery enabled us to identify further organizations that had been targeted by WastedLocker and identify additional tools, tactics, and procedures used by the attackers, helping us to strengthen our protection against every stage of the attack.
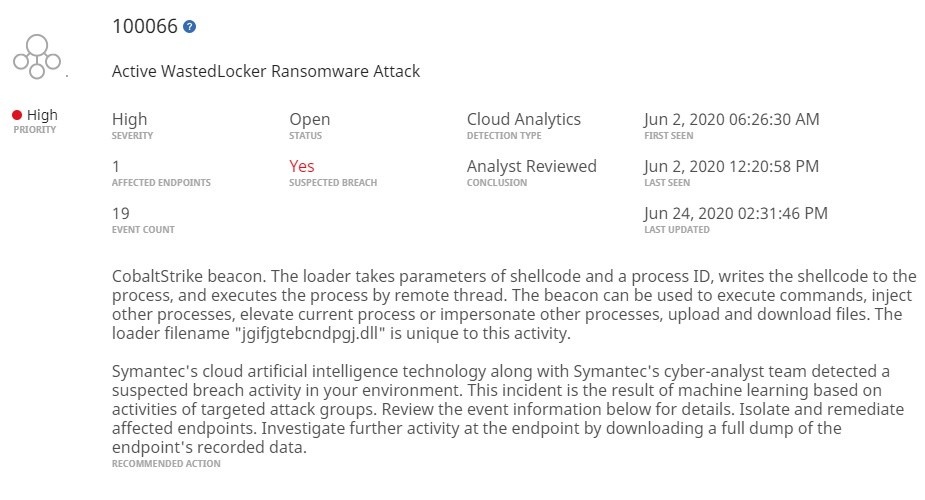
Figure 1. Example of Targeted Attack Cloud Analytics alert received by Symantec Endpoint Detection and Response (EDR) customers, warning them of early stage WastedLocker activity on their networks
Read the entire article here

