
by Anastasios Arampatzis
The SolarWinds hack was an extremely serious compromise of the United States’ infrastructure. Industries and critical infrastructures are increasingly dependent on digital technology. Their openness, interconnectivity, and interdependence on supply chains has created a large threat and attack surface, which adversaries are eager to probe and exploit.
What are supply chain risks?
First, let us define what a supply chain is. A supply chain is a network of people, processes, technology, information, and resources that delivers a product or service.
A supply chain risk is a function of threat, vulnerability, and consequence. A supply chain threat is specific and credible information that a component, system, or service might be targeted by adversaries. A vulnerability is a weakness which is either inherent to the component, system or service, or has been introduced by an outside agent.
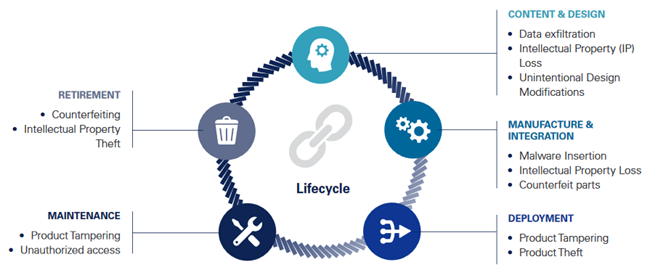
Figure 1: Supply Chain Risks. Source: National Counterintelligence and Security Center (NCSC)
A supply chain risk is when the capability and intention of an adversary aligns with the opportunity to exploit a vulnerability. The consequence of this would allow the adversary to extract Intellectual Property (IP), sensitive government data, and personally identifiable information. Further, such an action may allow an adversary to surveil, deny, disrupt, or otherwise degrade a component, system, or service. These actions may compromise the integrity, trustworthiness, and authenticity of critical services and products.
Are supply chain attacks a threat to national security?
The primary incentive behind supply chain attacks seems to be surveillance: to see who is connected to whom, what they say, how they say it and when they communicate with each other. But we must be prepared for more malevolent actions targeting the very critical infrastructure of every nation. While the primary results of a supply chain attack might not be immediately visible, imagine what could happen in a real kinetic conflict, where physical incursion could be used by adversaries to inflict real damage to critical infrastructure.
Considering our increased reliance on SCADA (Supervisory Control and Data Acquisition) systems that digitally manage manufacturing, transportation, power generation and large-building infrastructure, severe damage can be caused by something as simple as programming a gauge to give false readings or turning off a circuit or circuit breaker.
We have already witnessed the impact and the consequences of cyber-attacks against critical infrastructure with the Stuxnet cyber-attack on the Iranian Natanz uranium enrichment facility more than a decade ago. If an equivalent or larger attack on any developed country were to succeed, it would literally wreak havoc on all daily activities: no email, no phones, no electricity, no water, no fuel, no money. Such an action would be an attack against the so-called “Center of Gravity” and would paralyze the country’s backbone and would disable the country’s ability to respond.
Dan Geer, a senior fellow at In-Q-Tel (the non-profit venture capital arm of the CIA), said commenting on the consequences of supply chain attacks that “That’s the very definition of asymmetric warfare.”
The digitalization of the critical infrastructure such as the electric grid and the water supply is threatened by cyber-physical vulnerabilities, which make the management of supply chains a question of national security. However, the problem is not the lack of tools to detect anomalous behaviors on corporate or government networks. It is rather the lack of a consistent and coherent plan to do so. The SolarWinds attack profoundly demonstrated “how hard it is to find and interdict attacks at cyberspeed,” as Retired Brig. Gen. Greg Touhill, who was appointed by President Barack Obama as the government’s first chief information security officer, wrote in a recent Appgate blog.
It is high time that we got serious about supply chain risk management.
Supply Chain Risk Management (SCRM) best practices
Supply Chain Risk Management (SCRM) is the process of identifying, assessing, and mitigating the risks to the integrity, trustworthiness, and authenticity of products and services within the supply chain.
An effective SCRM program should focus on three areas:
- Enhance capabilities to detect and respond to supply chain threats.
- Advance supply chain integrity and security across the organization.
- Expand outreach on supply chain threats, risk management, and best practices.
For an SCRM program to be effective, it should contain the following elements:
- Obtain executive level buy in and commitment.
- Communicate the plan with all involved stakeholders.
- Identify, assess, and classify critical assets, processes and suppliers.
- Identify, assess, prioritize, and implement adequate controls to reduce the risks.
- Elevate security as a metric just like performance to assess a vendor’s ability to meet contractual requirements.
- Conduct due diligence on suppliers.
- Monitor suppliers’ compliance with defined security requirements.
- Establish processes for information sharing with suppliers about vulnerabilities.
- Manage security risks when terminating contracts with suppliers.
- Monitor effectiveness of established risk mitigation strategies, revise and update as required.
- Educate employees on managing, mitigating and responding to supply chain risks.
- Plan for business continuity and exercise contingency plans.
How ADACOM helps you mitigate supply chain risks
The sophistication of modern cyberattacks, the persistent nature of advanced threats, and the importance of managing business risk on a continual basis requires enterprises to reevaluate their entire security ecosystem. It’s now critical that security analytics include a detailed analysis of information on users, attacks, context, time and location from identity, endpoints, servers, apps, web and email servers, and non-traditional systems.
ADACOM’s analytics-driven security solutions provide a comprehensive approach to cybersecurity, including advanced techniques like machine learning and behavioral analytics. These techniques help security teams quickly identify, investigate, and respond to threats based on a broader security context than is possible with legacy security products. Security Analytics solutions can be deployed on-premises, in the cloud or in a hybrid cloud deployment.
Notis Iliopoulos, GRC & Assurance Director, stated:
“Managing supply chain risk is a very challenging task due to the extended ecosystem of the modern supply chain.
In order to better manage supply-chain risk, ADACOM has a vast offering targeting Supply Chain Security Risk Management, which is summarized next.
Adoption of a holistic framework for managing information security. The framework extends the traditional Information Security & Risk Management model provide information assurance to protect all types of sensitive information, in all phases of the information lifecycle throughout all business verticals, regardless of the underlying business and technology ecosystem.
Risk Assessments to measure supply chain risk, enabling your organization to assess their internal controls and collect relevant supporting documentation for further analysis. Risk Assessment is targeting specific supply chain threats and vulnerabilities, and the results are factored into a determination of the residual risk of each engagement being delivered by the third party.
Automation of assessment via GRC tools & solutions. ADACOM partners with RSA in order to provide Third Parties Management Automation via RSA Archer. The RSA Archer® Third Party Governance use case provides supplier engagement performance monitoring. Metrics can be established within four categories: Quality, Innovation, Performance, and Relationship. Metrics are depicted for each engagement and rolled up to the third party to depict their performance across all of their product or services engagements with your organization.
Development of a Supplier Management Security plan, which includes supplier criticality assessment and contractual cybersecurity requirements.
Incident response and continuity. Calibration of the existing incident response processes and technology in order to be ready to respond to supply chain specific incidents. While incident response is the first step in establishing continuity, a proper Business Continuity Plan is needed, that is also addressing business disruption due to supply chain risks.
Last but not least, ADACOM utilizes technology & consulting services in order to create & support Information Security Awareness campaigns. “
To learn more, contact our experts.
