
by Anastasios Arampatzis
During the last days of 2020 and the first days of 2021, the cybersecurity news were flooded with the apocalypse of the SolarWinds supply chain attack. Now that the dust begins to settle, it is a good time to reflect on the event and see what we can learn from that.
But first, a quick overview of the attack.
What actually was the attack?
To cut the long story short, malicious actors got inside the development operations of SolarWinds and managed to insert malware inside a software update that was distributed by the company in March. Once installed, the malware “called home” to the attackers’ command-and-control center, which enabled them to enter the network and take further action.
To achieve their purpose, the criminals deployed three malware strains, namely Sunspot, Sunburst and Teardrop. According to ZDNet, the Sunspot malware was installed on SolarWinds build server that assembled Orion, one of SolarWinds’ top products. Once a build command was detected, the malware would silently replace source code files inside the Orion app with files that loaded the Sunburst malware, resulting in Orion app versions that also installed the Sunburst malware. Since the patch came from the company and was digitally signed by SolarWinds, few companies would have known their software was compromised.
The Sunburst malware would activate inside internal networks of companies and government agencies, where it would collect data on its victims and then send the information back to the SolarWinds hackers. Threat actors would then decide if a victim was important enough to compromise and would deploy the more powerful Teardrop backdoor trojan on these systems while, at the same time, instruct Sunburst to delete itself from networks it deemed insignificant or too high risk.
SolarWinds published on their blog a timeline of how the events unfolded. According to the company, the threat actors executed a test run between September and November 2019.
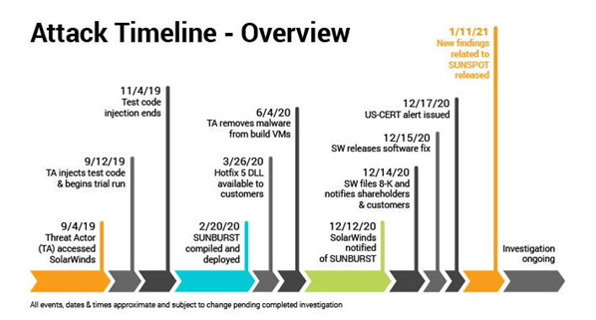
Figure 1: SolarWinds attack timeline. Source: SolarWinds
What are the lessons learned?
When we fail to defend against a cyber-attack, we tend to say that it was a “sophisticated” attack. The term “sophisticated” has been used so widely that its meaning has diminished. However, this is not the case with the SolarWinds. This attack was indeed an advanced and sophisticated one. The good thing is that the ongoing investigation by top cybersecurity firms provides some valuable lessons learned for all of us.
Lesson 1: Software supply chain management
Justin Sherman and Fred B. Schneider note that supply chain attacks are “Attacks that exploit new vulnerabilities an attacker introduces during development or manufacture but before deployment.”
Enterprises and vendors must consider the risk introduced by supply chain attacks and adapt and evolve both strategically and tactically. Organizations should create a “cyber kill chain” for supply chain compromises, placing barriers in the attackers’ path to prevent, disrupt, or detect such incidents before the software gets weaponized against them causing damages.
Preventing supply chain attacks starts with establishing governance over the organization’s supply chain. The reality is that most organizations do not have visibility or control over the security practices of their third-party vendors. This lack of control creates security gaps which can be exploited by adversaries to launch their operations.
Organizations should seek to improve software supply chain governance by creating a baseline of software security best practices that serve as requirements that software vendors must comply with. Industry best practices for secure Software Development Lifecycle (SDLC) should be the starting point for any software supplier. These practices should include processes for code sourcing, code review, and consistent software security testing. Additionally, the SDLC policies should detail practices to detect anomalous code insertions like the one that affected SolarWinds and may go undetected by traditional security measures.
Lesson 2: Indicators of Compromise have limitations
The SolarWinds campaign also highlights the limitations of indicators of compromise (IOC). FireEye’s detailed report shows that the attackers did not use previously known infrastructure or malware exploits. If the compromise detection strategy is based on known bad indicators, organizations will not be able to detect an attack like this. Malware strains were used strategically to achieve predefined objectives, such as stealing credentials. The stolen credentials and “traditional” remote access were leveraged to launch the next steps of the attack. Looking for known “bad indicators” is not sufficient for this kind of scenario.
Lesson 3: Use analytics for threat detection
The SolarWinds use case underscores the importance of using analytics for threat detection. The attackers’ actions were focused on avoiding detection by known threat detection solutions and practices. They were keen on avoiding detection based on IP geolocation anomalies or on command-and-control beaconing behavior.
This does not mean that traditional threat detection is no longer effective. It implies, however, that it has to be supplemented by behavioral analytics. Behavioral analytics supercharges threat detection by using machine learning, statistical analysis, and behavioral modeling to correlate and enrich events.
Nevertheless, the real lesson on threat detection is that these advanced attackers were paying attention to what blue teams are doing and adjusted their tactics to avoid detection.
Way ahead
“The recent interest in defending against supply chain attacks should not be surprising,” highlight Sherman and Schneider. “Nations are increasingly coming to depend on networked systems for commerce and for defense. Attacks by foreign threat actors on domestic suppliers and domestic use of foreign suppliers raise questions about national security,” they conclude.
The sophistication of modern cyberattacks, the persistent nature of advanced threats, and the importance of managing business risk on a continual basis requires enterprises to reevaluate their entire security ecosystem. It’s now critical that security analytics include a detailed analysis of information on users, attacks, context, time and location from identity, endpoints, servers, apps, web and email servers, and non-traditional systems.
ADACOM’s analytics-driven security solutions provide a comprehensive approach to cybersecurity, including advanced techniques like machine learning and behavioral analytics. These techniques help security teams quickly identify, investigate, and respond to threats based on a broader security context than is possible with legacy security products. Security Analytics solutions can be deployed on-premises, in the cloud or in a hybrid cloud deployment.
ADACOM’s consulting services could assist Organizations to assess the cyber security risks, related to their supply chain, and propose the required countermeasures.
To learn more how you can benefit, contact our experts.
