by Anastasios Arampatzis
Greece is about to become an energy hub for the European Union. The Trans Adriatic Pipeline (TAP) and EastMed pipeline will transport much needed natural gas to the industries and homes of the EU member states in the framework of minimizing CO2 emissions and mitigating the climate change effects.
Cyber threats to Oil and Gas industry can disrupt the national economy
Despite the importance of these projects, new security concerns and challenges are introduced that need to be addressed sooner than later. The challenges concern both physical and cyber related threats. When it comes to physical threats, EGIG (European Gas pipeline Incident data Group) reported a total of 1366 incidents from 1970-2016, the leading causes being Third Party Interference (TPI), such as ground works, malicious acts and sabotages, and ground movements. On the other hand, although the number of cyber incidents reported so far is less, the results can be devastating as well. Attacks such as Night Dragon and Shamoon have caused considerable financial damage to oil and gas companies.
Oil and Gas, like other critical infrastructure environments, rely on highly reliable Industrial Control Systems (ICSs) and supporting infrastructure. The consequences of cybersecurity breaches, such as station shutdown, utilities interruption, production disruption, impact to the environment through detected or undetected leaks, and even the loss of human life, make cybersecurity a critical area of concern within industry. For this reasons, Oil and Gas industry is among the national critical infrastructures described in the European Union Network and Information Systems Security Directive (NIS Directive).
A 2017 study found that industrial cybersecurity is difficult for even the most technologically advanced Oil and Gas companies for a variety of reasons:
- Long life cycles of operational assets
- Inaccurate and outdated asset technology inventories
- 24/7/365 continuous operation times (barring turnarounds and shutdown)
- No single approach to security in the regulations or standards
These factors coupled with a rapidly evolving technological landscape pose a serious risk to the industry. This is not merely a concern for the future, but a current reality. Another study by Kaspersky found that 68% of respondents to an Oil and Gas survey admitted that their organizations had experienced at least one cyber compromise. For large organizations, the same study found that there were two to five such incidents per organization.
A recent SANS Institute report found that four out of ten organizations lack appropriate visibility into their ICS networks to monitor assets and operations to identify potential threats. This creates the risk of not being able to recognize and respond to attacks. How do you secure what you do not understand?
The potential for disruption and damage from cyberattacks is real and a threat that the Oil and Gas industry must proactively address to protect the critical infrastructure of a foundational economic industry.
Cybersecurity is a top priority
Cybersecurity should be a top priority for the natural gas and oil industry. Industry companies must take seriously the protection of industrial control systems (ICS) and operational technology (OT) – the digital monitoring and/or controls of physical assets – and prevent energy disruptions that can impact national security and public safety.
The Oil and Gas industry faces the threat of cyberattacks from a variety of malicious actors including nation states, criminal organizations and bad actors seeking to steal intellectual property and/or compromise industrial control systems (ICS), among many other nefarious goals.
The industry has witnessed the evolution and sophistication of such cyber criminals as well as the advancement of their techniques, tactics and procedures (TTPs), moving from manual operations to more sophisticated and wider-spread machine-to-machine and artificial intelligence automated attacks. There are multiple other attack vectors including insider threats, attacks via supply chain tampering or disruption, and insertion via counterfeits. Cyber threats may be exacerbated through combination with physical attacks or execution during a natural hazard disruption.
Industry companies recognize that they and their assets are the targets of an increasing number of cyberattacks, and protecting these assets is a significant priority. Industry infrastructure is highly automated, and pipeline operators, terminal owners and utilities alike rely on ICS for monitoring and/or remote control.
ICS are not unique or new to pipelines and are prevalent across the energy system, including at coal and nuclear plants. The digital controls of industrial facilities include supervisory control and data acquisition (SCADA), process control networks (PCN) and distributed control systems. These systems keep operations up and running. Advanced cybersecurity operations are critical to ensure that ICS –particularly those operating critical infrastructure – are segmented and thus protected by limiting exposure to attack.
A “defense-in-depth” approach
In recognition of the sophistication of cyber attackers, and the enterprise risk presented by cyberattacks, natural gas and oil companies have developed comprehensive risk-based “defense-in-depth” approaches to cybersecurity similar to industry’s approach to managing the other enterprise risks: robust governance, systematic risk-based management, and multi-dimensional programs based on best-in-class standards and proven frameworks.
There are various standards and frameworks that dictate Oil and Gas facilities, pipelines, and ICS security in general:
- ISA/IEC 62443 Industrial Control System standard
- API 1164 Pipeline Supervisory Control and Data Acquisition (SCADA) Security standard
- NIST 800-82 Guide to Industrial Control System Security
- IEC 27019 Security Management for Process Control
- Chemical Facility Anti-Terrorism Standards (CFATS)
IEC 62443 is the most widely adopted cybersecurity standard globally for ICSs and is the de facto standard in the Oil and Gas industry. The Purdue Model for Control Hierarchy also describes a hierarchical data flow model, where sensors and other field devices are connected to the ICS. The ICS serves the dual purpose of controlling processes or machines and serving processed data to the operations management level of applications. Level 3 applications feed information to the enterprise business system level.
Regardless of the structure used for cybersecurity program development, natural gas and oil companies typically buffer ICS from cyberattacks through the use of “defense-in-depth” network architecture. Natural gas and oil companies segment their systems and implement “demilitarized zones” (DMZ) between industrial controls and internet-facing business networks.
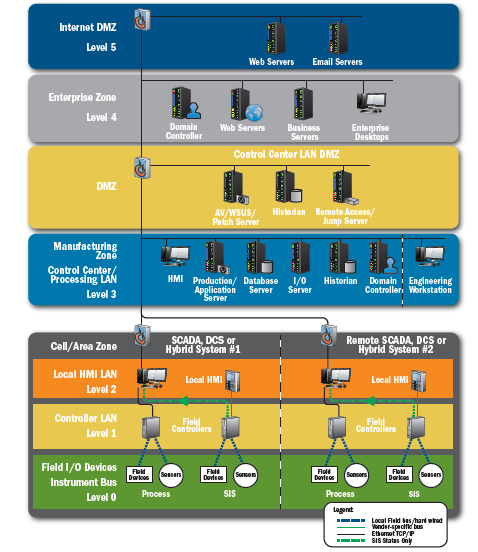
Figure 1: “Defense-in-depth” architecture in line with the Purdue Model. Source: American Petroleum Institute.
The ISA/IEC 62443 standards provide ICS operators with:
- A framework for network architecture, including segmentation through zones and conduits.
- Guidelines for companies to put into place a security management system, conduct patch management, and establish internal cybersecurity requirements for suppliers.
- Guidance to companies for deployment of cybersecurity technologies, ICS security risk assessment and system design, and internal requirements for ICS security and cybersecurity levels.
- Guidance to companies for internal requirements for product development and technical security of ICS components
Technology, People and Processes
The traditional model has focused on segmentation and restricted traffic flows, but this is not enough to secure an operational domain. More recently, the National Institute of Standards and Technology (NIST) Cybersecurity Framework—with its charter to protect critical infrastructure—has strongly emphasized the human component of cybersecurity.
The reality is that technology itself can only address about half of the cybersecurity threat, whereas people and processes play a critical part in every aspect of threat identification and monitoring. This means that guidelines and standards are not concrete measures to provide protection but do provide a solid foundational base from which to work. The most comprehensive approach to securing the Oil and Gas industry combines technology, people, and processes, both cyber and physical.
A properly designed standards-based architecture to secure use cases and systems, bringing together the operational (Levels 3 and below) and enterprise (Levels 4 and above) domains, is critical. The architecture should provide an understanding of all components of a use case, map these elements together in a structured way, and show how they interact and work together. A properly designed architecture not only brings together IT and OT technologies, but also includes vendors and third-party content; in other words, it secures the ecosystem. Gartner believes that
security can be enhanced if IT security teams are shared, seconded, or combined with OT staff to plan a holistic security strategy.
This approach creates a landscape that is much more challenging for an attacker to fully penetrate –providing necessary time to implement defensive response measures. A layered defense approach also incorporates system redundancies and fail safes including the ability to manually operate without ICS.
The ADACOM way to secure the Oil and Gas industry
Adoption of standards & best practices is just the first step. The Oil and Gas sector has a specific threat profile, that is a mix of threats and risks related to the business needs of the sector, as well as, the relation to safety issues, and the entanglement of ICT & Operational Technology.
The Oil and Gas industry should follow a holistic approach towards the protection of its assets and critical infrastructure. To do so, ADACOM propose the adoption of the following:
- Holistic approach to Security Risk Management (addressing all applicable digital, physical, hybrid risks)
- Risk mitigation based of processes and technology tailored to the Oil and Gas sector
- Adoption of a continuous risk and effective assessment process
- Development and enforcement of an Information Security Management Systems, based on the concepts of information resilience
- Selection & Adoption of the required cyber security technology in order to effectively defend against cyber attacks
- Awareness tailored to the needs of the sector
ADACOM can also help Oil and Gas organizations to safeguard their critical assets and be resilient against cyber incidents through a comprehensive risk management and cyber security technology adoption program.
You may learn more by contacting our experts.
